OUR SERVICES
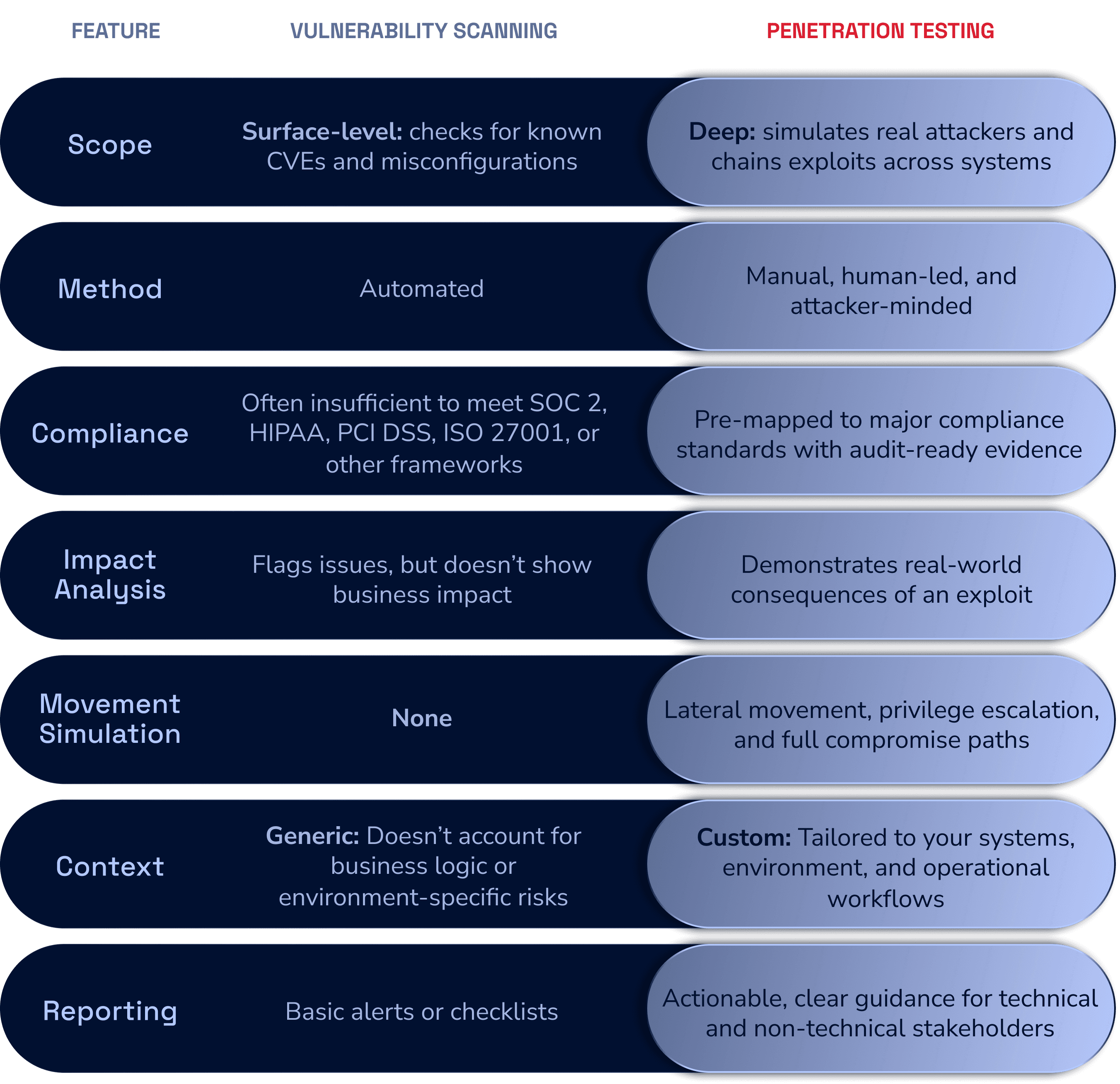
Our approach covers the full spectrum of risk. For most organizations, this starts with our core Penetration Testing for web, network, and cloud assets to meet SOC 2 and ISO standards. For mature security teams, we offer advanced Red Teaming and adversary simulation.
Protect the systems your users rely on every day:
Web Application Penetration Testing
Simulates attacks against your public or internal-facing web apps, APIs, and portals to uncover vulnerabilities like XSS, SQLi, and privilege escalation paths
Mobile Application Testing
Assesses your iOS and Android apps to uncover flaws like insecure data handling, API abuse, and authentication bypasses
Desktop Application Testing
Evaluates your Windows, macOS, and Linux applications to uncover risks like insecure data storage, privilege escalation, and vulnerable libraries
Source Code Review
Analyzes your application source code line by line to uncover logic flaws, injection risks, and insecure coding practices
Attackers are continuously probing your infrastructure. We simulate how they would get in, what they would do next, and what they would find:
External Network Penetration Testing
Test public-facing IPs and services without credentials, just like a threat actor would; ideal for catching misconfigurations before they’re exploited
Internal Network Penetration Testing
Simulate threats originating from stolen credentials, insider threats, or compromised devices to understand your internal risk landscape
Segmentation
Simulate attacker movement between segments to confirm isolation is working as intended and identify misconfigurations that could allow unauthorized access
Wireless Penetration Testing
Identify critical Wi-Fi risks including rogue access points, insecure encryption, and insufficient client isolation
Gain visibility and security assurance in cloud environments such as AWS, Azure, and Google Cloud. We test for:
Excessive IAM permissions
Publicly exposed buckets or services
Misconfigured policies
API gateway vulnerabilities
Privilege escalation risks
Go beyond standard penetration testing with a full adversary simulation:
Initial Access Vectors:
Phishing, credential reuse, and other real-world intrusion tactics
Lateral Movement & Privilege Escalation:
Can we achieve domain admin?
Command & Control:
Safe simulations of persistence and data exfiltration
Operational Impact Reports:
Get a real insights into potential damage
Because the weakest link is often human:
Phishing
Custom email attacks to test staff awareness and response
Vishing
Phone-based attacks to test staff handling of sensitive info
Smishing
Text-based simulations replicating actual attacker methods
When standard testing isn’t enough, our advanced assessments dig deeper into specialized security challenges and emerging threat landscapes:
Blockchain & Smart Contracts
LLM/AI Testing
Threat Modeling
Risk Assessments
Tabletop Exercises
Purple Teaming
Pentest Plus
Personal Penetration Testing
Physical Penetration Testing
Our PTaaS platform comes standard with every test. It’s how we turn penetration testing from a static, fragmented process into a streamlined, transparent security function.